Table des matières
Renewal of VPN certificate
If you have issues connecting to the VPN and you see the error:
Certificate has key usage 00a0, expects 00a0
in /var/log/openvpn-client.log, then your certificate has probably expired.
To check its expiry date, as root type the command:
- snippet.sh
$ openssl x509 -in /etc/openvpn/keys/user.crt -noout -enddate notAfter=Nov 12 13:42:43 2018 GMT
The displayed date after noAfter is the expiry date.
There are four methods to renew the certificate.
1. Neutrinet app
The Neutrinet app takes care of checking every night whether certificates must be renewed.
Install
You can either install the app through the admin panel, or with:
- snippet.sh
yunohost app install neutrinet
Upgrade
To upgrade this app:
- snippet.sh
yunohost tools update apps yunohost app upgrade neutrinet
2. From a cube
If the Neutrinet app is already installed, you can force the certificates verification:
- snippet.sh
/opt/neutrinet/renew_cert/renew_cert.sh
3. From the renew_cert script
Clone the following git repository, either on your cube or your own computer:
- snippet.sh
git clone https://git.domainepublic.net/Neutrinet/renew_cert
Move to the folder that just has been created:
- snippet.sh
cd renew_cert
Create a virtual python3 environment. This means that the installed python3 packages won't have any impact on the rest of the system:
- snippet.sh
python3 -m venv ve
Enable this environment:
- snippet.sh
source ve/bin/activate
Install the script dependencies:
pip install -r requirements.txt
Finally, run the script with this command:
python renew.py <Neutrinet VPN's username>
You will be asked for your password to login to the Neutrinet VPN.
Normaly, a subfolder named certs_YYYY-MM-DD_HH:MM:SS (replace the uppercase letters with the script execution date and time ) should be created, which contains all the configuration files needed for the OpenVPN client.
The files that we need are client.crt, client.key, and ca.crt, i.e. the public and private key of the client certificate, and the public key of the server certificate.
These files must replace the files in /etc/openvpn (this may change depending of the OS).
On the cube, these files are in /etc/openvpn/keys
Remark: Before replacing one with the other, it is advisable to make a backup of the old certificate, just in case. For instance, with the following commands (still from the renew_cert directory):
- snippet.sh
sudo mv /etc/openvpn/keys/user.crt{,.backup} sudo mv /etc/openvpn/keys/user.key{,.backup} sudo mv /etc/openvpn/keys/ca-server.crt{,.backup} sudo mv client.crt /etc/openvpn/keys/user.crt sudo mv client.key /etc/openvpn/keys/user.key sudo mv ca.crt /etc/openvpn/keys/ca-server.crt
All you need to do is to restart the OpenVPN service to check if it's still working.
Remark: Ideally, make sure to be connected on the same local network as your cube, i.e. through its local address (192.168.1.x in most cases).
- snippet.sh
sudo systemctl restart ynh-vpnclient`
You can check that everything went well by looking at the logs:
tail /var/log/openvpn-client.log /var/log/ynh-vpnclient.log
4. From user.neutrinet.be
This method sometimes requires some patience because user.neutrinet.be can produce some failures.
Login with ssh to your internet cube, then go to the folder where the VPN key is located (it should be the file /etc/openvpn/keys/user.key):
- snippet.sh
cd /etc/openvpn/keys
Create a certificate signing request (CSR) for this key:
- snippet.sh
openssl req -out client.csr -new -newkey rsa:4096 -nodes -keyout user.key
You will be asked for several questions, such as the country code (BE), the region (Bruxelles, …), the organisation, etc… to which the certificate is related.
Most important is the Cname, that is the name which will be used by Neutrinet to know to whom belongs the certificate.
Remark: It is recommended to provide your email address for the Cname field.
This command create a file named client.csr, which contains the certificate signing request. You can display its content with:
- snippet.sh
cat client.csr
Copy this content, then go to https://user.neutrinet.be
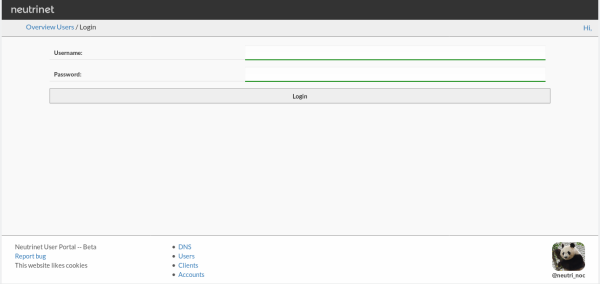
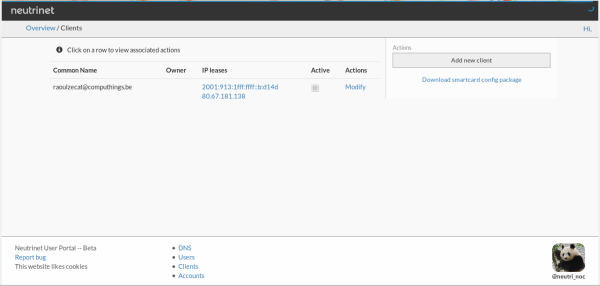
Login
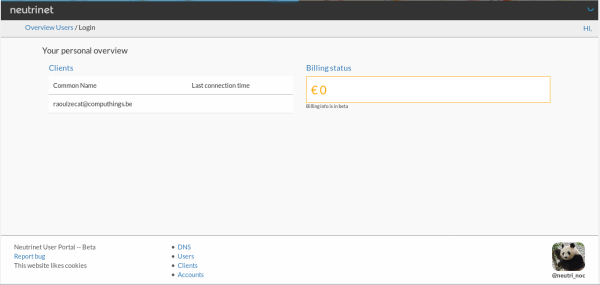
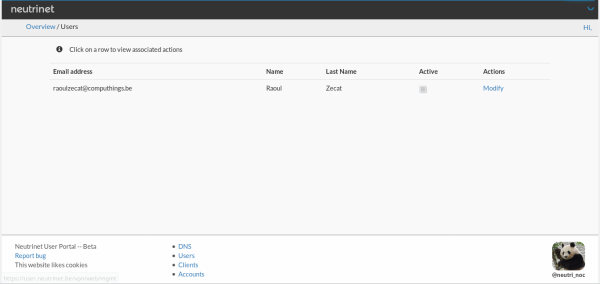
Click on Users
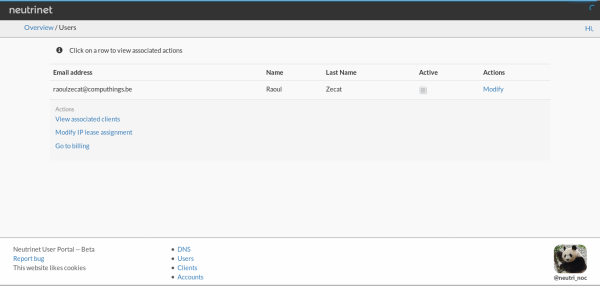
Wait for the page to load, and when you see your name click on it.
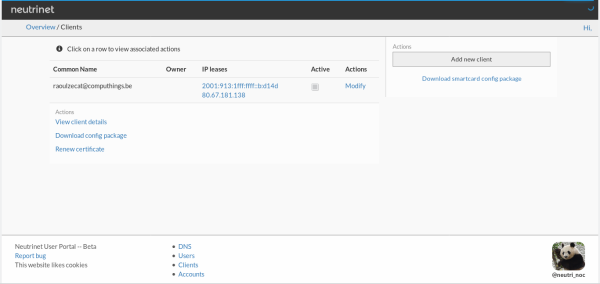
Click on View associated clients
Click on your certificate (if you have more than one, use the one with an IPv4 - 80.67.181.x)
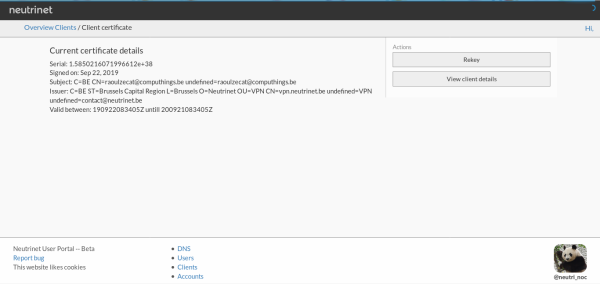
Choose the Renew certificate option
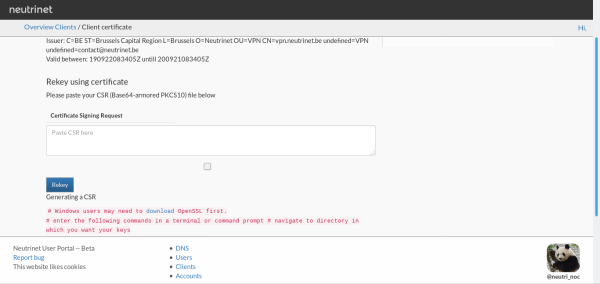
The current certificate should appear on the screen. Click on Rekey, then paste the content of the CSR (the file you copied earlier).
Click on the Rekey button to confirm.
Once this operation done, you should see the following banner:
You can click on View client details, then on Download config package.
This will download a zip file containing the certificate files. In the directory /etc/openvpn/keys of your cube, copy the file client.crt to /etc/openvpn/keys/user.crt.
That's it!